Are Smart Factories Secure?
December 12, 2017

Manufacturers are adopting Smart Factory technologies that connect devices, production systems, processes and even entire factories in networked ecosystems that are more intelligent, adaptable and self-aware. The goal: actionable insights that can be used to increase productivity, make production processes more agile and generate new “outcome-based” revenue streams. But are smart factories secure?
This digitization of the factory is part of an overall trend toward digital transformation that no modern industrial enterprise can ignore and remain competitive. However, moving from a closed, siloed factory environment to an open, connected model carries with it risks. As with corporate IT systems, connected factories are by their nature more vulnerable to security attacks that are not present in a closed environment. Regardless of the type of security attack, the results can be devastating, culminating in lost production cycles, wasted material, potential harm to personnel, loss of revenue and more. As a result, industrial enterprises face a tough decision: move forward with their digital transformation initiatives or play it safe and be left behind.
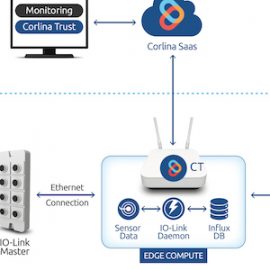
Any practical and useful implementation of a security solution must span the entire IIoT stack on the factory floor. This means that the advanced security principles are incorporated as an integral part of the solution and applied at each step in the deployment of connected devices. In today’s modern Smart Factory, numerous sensors and cameras are deployed on the factory floor, which increases the attack surface.

As these devices are physically exposed, their software can be tampered with to cause a major system meltdown (DDoS attacks). A lack of end-to-end visibility in the IIoT stack is dangerous and makes these attacks difficult to detect. To prevent this kind of attack, the first step to introducing any security measure is to provide visibility in as many areas of the factory as feasible. Securing actuators in the factory network is a high priority since the output of the actuator controls sensors and other actions or processes. An attack targeting an actuator can cause havoc to the production workflow.
Since it is a relatively simple task, anyone with a few technical skills can introduce a sensor or camera into the network. However, deploying devices that do not meet the compliance policies of the organization is a huge security threat. Corlina’s Smart Factory System of Trust provides full visibility as data moves through the stack, including device information, data collection, data transport and network state. To learn more about how we help manufacturers go beyond security to establish trust, contact us at info@admin.site.corlina.com today.
Related articles
We were very excited to learn on Friday that the Corlina System of Trust has received a 2019 IoT Evolution Industrial IoT Product of the Year Award from IoT Evolution World, the leading magazine and Web site covering IoT technologies. It’s very exciting when your product receives this type of
In our recent articles, we’ve talked about taking a different approach to embarking on building IIoT capabilities, one that protects organizations from pilot purgatory by focusing on a specific challenge in the manufacturing environment and yielding ROI quickly. It’s not a rip-and-replace method requiring massive investments in new equipment. It’s
Solution Overview Corlina’s brownfield monitoring solution blueprint is intended to enable monitoring and decision-making based on information captured from already-in-place equipment. These existing systems are often implemented on closed architectures and/or closed data buses for reliability reasons, or they may not include any embedded sensors whatsoever. Corlina provides a cost-effective